Weak passwords are often the cause of data breaches. Love or hate them, everyone is using passwords today. Ensuring individuals are using strong passwords in important to securing an organization. Whether you’re performing a penetration test or a password audit, tools can help you add value and efficiency for your report. At Stern Security, we […]
Vendor Risk Management Accuracy is all that Matters! Many organizations utilize spreadsheets to measure their internal security posture and vendor risk. We get it – spreadsheets are simple, convenient, and it comes with the office suite that you have on your computer. Unfortunately, it does not scale and gets out of hand quickly. Let’s look […]
Duo Security is one of the most popular 2-factor authentication applications on the market today. All of the authentication and administrative logs are stored in the admin portal located at https://admin.duosecurity.com. Up until recently, if you wanted to view the logs, you either had to log into the admin portal or use the Duo API […]
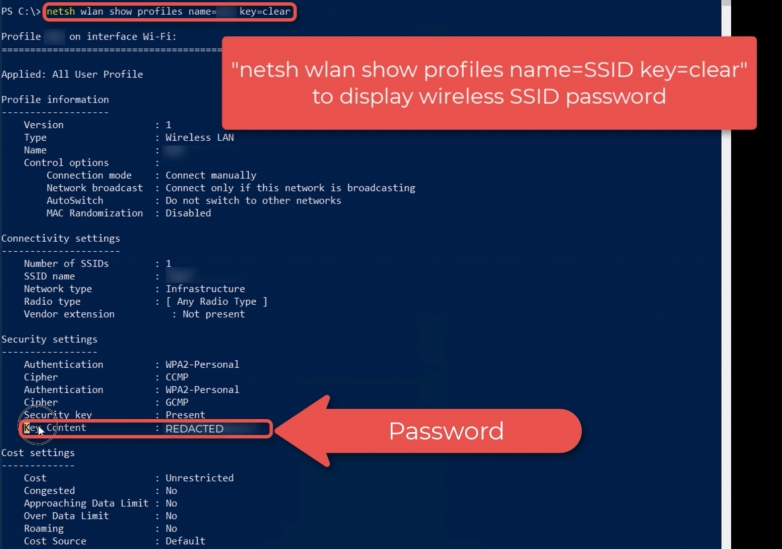
Without using any 3rd party tools, you can use simple Window commands to display the saved passwords for remembered wireless networks. This is helpful if you forget or during security engagements. Stern Security gained access to a laptop on a recent penetration test. We needed to gain access to a particular wireless network didn’t want to risk tripping […]
One would think that most data breaches were caused by hacking as those are the breaches that are always mentioned in the news. However, up until the end of 2019, Theft was still the top cause of breaches in healthcare according to data compiled from the U.S. Department of Health and Human Services (HHS) Office […]
Stern Security’s Founder and Principal, Jon Sternstein, presented at the 2019 NCHICA Incident Response 101 Forum. His presentation was titled, “Creating the Incident Response (IR) Plan Using Playbook Scenarios”. The full presentation can be read below. Presenter: Jon Sternstein August 2nd, 2019 Research Triangle Foundation12 Davis DriveResearch Triangle Park, NC
Background On January 22nd, 2016, the Food and Drug Administration released a draft guidance document titled “Postmarket Management of Cybersecurity in Medical Devices”. (Food and Drug Administration). This important document addresses the need for security throughout the lifecycle of several medical devices. Improving medical device security is a subset of President Obama’s February 19th, 2013 […]
Background How can an attacker capture usernames and passwords on a local network by simply waiting for the computers to willingly give them up? LLMNR and NBT-NS poisoning! Link-Local Multicast Name Resolution (LLMNR) and Netbios Name Service (NBT-NS) are two components of Microsoft Windows machines. LLLMNR was introduced in Windows Vista and is the successor […]